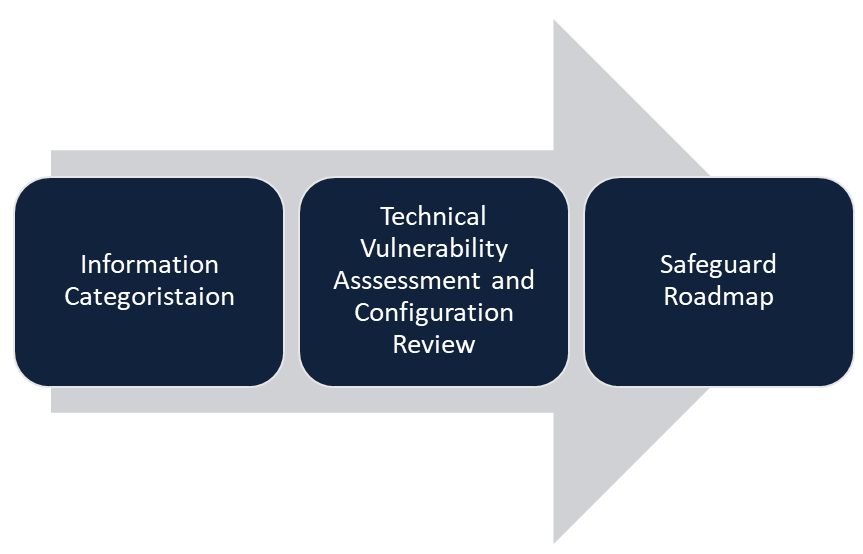
Cybersecurity Assessment
The Magnitude 8 Cybersecurity Assessment is intended to protect systems and information against the varied range of cyber threats that businesses face today. This involves identifying what needs to be protected, establishing where a business is currently vulnerable from a technical perspective and recommending safeguards that can be put in place to form a security baseline.
Information Categorisation
We start by identifying critical data and systems. We need to know what to protect and why. What is absolutely critical to your business? Who owns and manages this information? What would happen if this information was released to the internet or permanently deleted?
This step builds an asset register, an important business document that defines systems and information that is most critical to your business.
Technical Vulnerability Assessment and Configuration Review
The next step is to determine weaknesses in the environment from a technical standpoint. The systems that store and process the critical information will be reviewed from a security configuration perspective and scanned for vulnerabilities. This includes on-premises systems, cloud hosted servers, networking equipment, websites and Office 365.
Safeguard Roadmap
A prioritised roadmap of security controls which after implementation will form a security baseline, protect against cyber threats and address discovered vulnerabilities. These strategies will be prioritised to ensure that the essential controls that provide the most benefit and risk reduction are implemented first. The controls are based on the Australian Signals Directorate (ASD) and the National Institute of Standards and Technologies (NIST) control frameworks.
If you’d like to organise a meeting to find out more and meet our team, please contact us